Scammers Exploit Mobile Payments and Logins
Forwarding an SMS verification code can lead to a high phone bill. Scammers have discovered a way to exploit mobile payments, billed directly through your carrier. The same trick can be used to bypass two-factor authentication. They do not need access to your account or your password. Often, your phone number and your trust are enough.
TL;DR: Never Share an SMS Verification Code
- A scam can begin with nothing more than your phone number.
- A verification SMS is not just a formality. It confirms a payment or a login.
- By forwarding the code, you may authorize a mobile payment charged through your carrier or allow an attacker to access an account protected by two-factor authentication.
- The consequences can range from an unexpectedly high phone bill to losing control of your online banking or email.
One SMS Code and Thousands Gone
The process is surprisingly simple. The attacker first needs your phone number. They may find it in publicly available sources or request it under various pretexts, often through social media. Once the number is used to initiate a mobile payment, a verification SMS is sent to confirm the transaction.
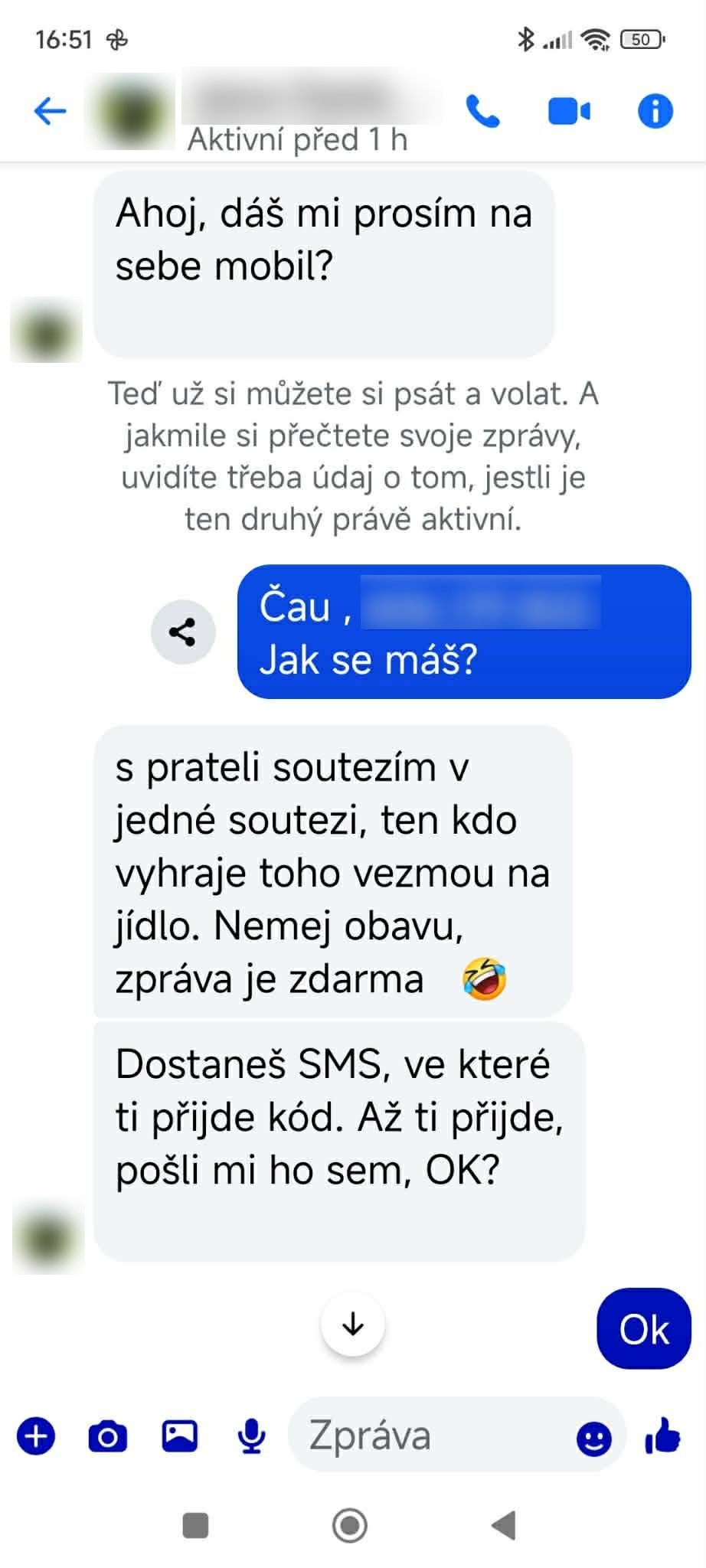
This is where manipulation begins. The scammer asks the victim to share the code. There are several common scenarios, such as a supposed contest win, a promised financial reward, or an urgent request to verify an account. The common goal is to create a sense of legitimacy and urgency that encourages the victim to respond without thinking. As soon as the code is forwarded, the payment is confirmed. The charge then appears on the mobile carrier’s bill or is deducted from prepaid credit.
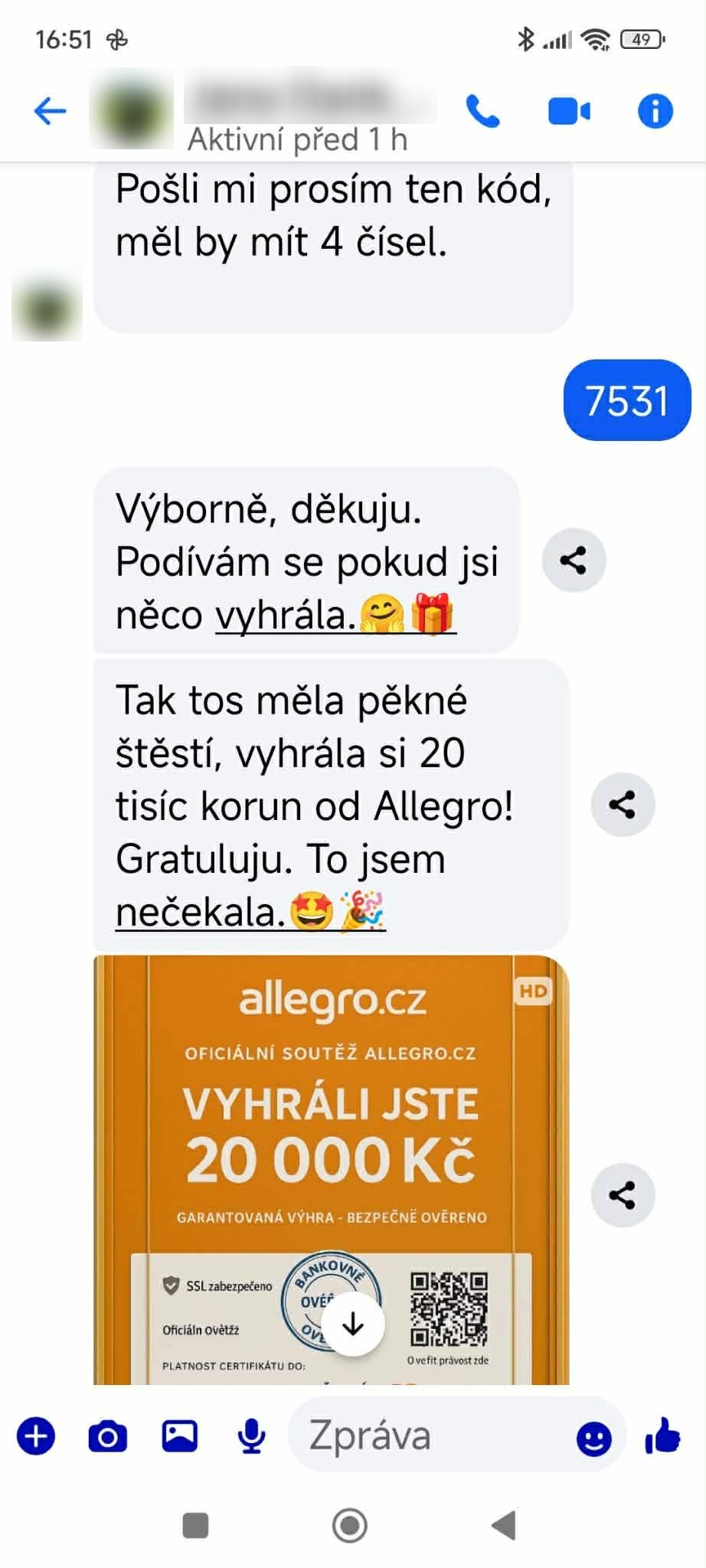
The success of these attacks is not based on technical complexity but on psychology. Scammers exploit trust, time pressure, and positive emotions, such as the promise of a prize. The message often comes from the account of someone the victim knows. That account may have been compromised earlier, for example after the owner entered their credentials on a phishing website. Once attackers gain access, they use the account to send messages to other contacts. As a result, the victim believes they are communicating with someone familiar rather than with a criminal.
The Same Trick with Two-Factor Authentication
The scam does not stop with mobile payments. The same approach can be used to bypass two-factor authentication, which is designed to add an extra layer of protection during login. In addition to a password, users must enter a one-time code that confirms their identity. However, if the user shares that code, the attacker can gain access to email, social media accounts, or other online services. Combined with additional information provided by the victim, this may even result in access to online banking. Two-factor authentication itself does not fail. The problem occurs when the account holder voluntarily shares the verification code.
If You Have Already Shared the Code, Act Quickly
- Contact your mobile carrier and request a review of mobile payments. Ask for the service to be blocked if necessary.
- Change the passwords for any accounts that may have been affected. If you reuse passwords, update them everywhere.
- Check your two-factor authentication settings to ensure that your phone number or backup email address has not been changed.
- Contact your bank if there is any risk that access to your account may have been compromised.
- Consider reporting the incident to the authorities.
Scams Are Constantly Evolving. Stay One Step Ahead.
- Stay informed! Read our blog and follow alerts in the app about the latest threats we’re monitoring for you.
- Our app Redamp.io includes a Safe Surfing feature that effectively handles protection against the latest threats such as phishing or malware.