Contactless payments under threat from ghost tapping
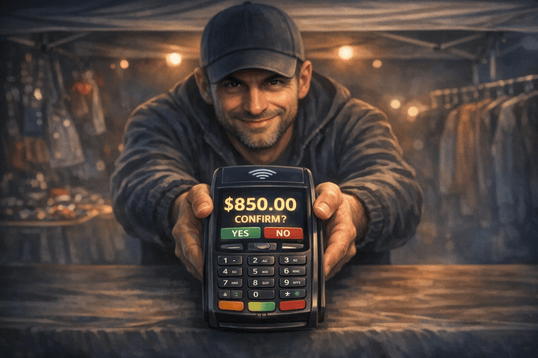
Contactless payments are a fast and convenient way to pay. A tap of a card or phone is all it takes to complete a transaction. However, fraudsters can exploit this convenience. Ghost tapping takes advantage of inattention, haste, and physical proximity. As a result, users may approve an unintended payment or pay a different amount than intended.
Summary: Ghost tapping is a scam that exploits the speed and simplicity of contactless payments
It often relies on inattention, where customers confirm a different amount than intended. Fraudsters may pose as legitimate vendors and pressure victims to pay quickly. More advanced attacks involve criminals first obtaining card details and then adding them to their own device. Using technology, they can relay the signal and make payments elsewhere without physically possessing the card.
Modern-day pickpockets
Ghost tapping exploits contactless payment technology, which operates over a very short range. Attackers therefore try to get as close as possible to the victim’s card or phone—typically in crowded environments where people are less aware of their surroundings. In some cases, a fraudster may attempt a small transaction simply by discreetly approaching the victim.
More commonly, however, the attacker poses as a legitimate vendor and relies on the speed of the interaction. The customer pays contactlessly without paying sufficient attention to the amount displayed on the terminal. At that moment, they may unknowingly approve a different payment than intended. These scams do not rely on complex technical methods but rather on haste, trust, and inattention. Ghost tapping is therefore not a traditional cyberattack, but a modern form of pickpocketing adapted to the digital age.

In addition to these scenarios, there are also more technically advanced methods of abusing contactless payments. Attackers first obtain card information, for example through phishing messages or fake websites. They then add the card to their own mobile device and can use it much like the legitimate owner. With specialized tools, they can even “relay” contactless communication to another device. In practice, this means someone can complete a transaction elsewhere without ever physically handling the card.
❗ Never enter your card details on unverified websites or apps, and do not respond to suspicious prompts.
How to protect yourself? Awareness is key
The good news is that protecting yourself against ghost tapping is straightforward. A few simple precautions can make a big difference:
- Keep your cards secure, ideally in a protective case or RFID-blocking wallet.
- Always check the amount and the merchant on the terminal before confirming a payment.
- Enable instant payment notifications to stay informed about every transaction.
- Regularly review your account activity.
- In higher-risk situations, consider inserting your card instead of tapping.
- Do not install apps from links sent to you.
- Never share your PIN or enter it into any applications.
Fraud is constantly evolving. Stay one step ahead
- Read our blog to learn about emerging digital threats and how they work.
- Follow in-app alerts about the latest threats, which we continuously monitor for you.